Download: pdf
The solution you need for continuous application security compliance.
The evidence you need for security audits & application risk management.
Features
- Accelerates compliance audits and ATO’s with automation and evidence – eliminates manual verifications with screen captures
- Pluggable architecture delivers a comprehensive compliance solution tailored to your highly custom application designs and deployments
- Provides out-of-the-box compliance controls and NIST 800-53 reports for OS, application servers, databases and cloud resources
- Continuously monitors and identifies mis-configurations between multiple environments at scale
- Provides root cause analysis to assist information Security, Configuration Management, DevSecOps, and Application Developers in identifying and remediating mis-configurations
U3C - Our Solution Model
Our model is a Unified Capitis Configuration Compliance (U3C) solution that connects all layers of security
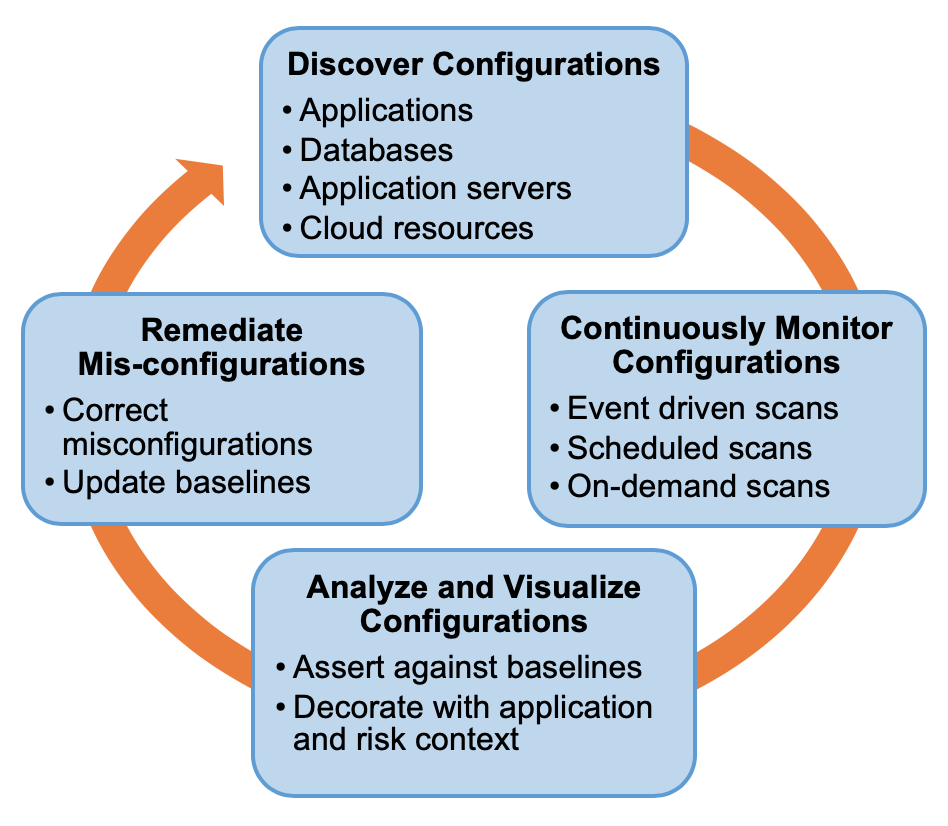
U3C Solution Model
At a major financial institution, our solution automates hundreds of thousands of compliance checks saving 1,000’s of hours of manual compliance efforts per year.
C2VS Use Cases & Value Proposition
ATO approval process
- Scan environment to be approved
- Provide evidence that configurations are correct
- Expedite the ATO process
- Eliminate manual effort & errors
Information Security Audits
- Scan production environments
- Analyze C2VS scan results
- Remediate any issues immediately
- 100% coverage verses manual spot checks
Continuous monitoring of production environments
- Trigger scans whenever configurations are changed
- Analyze results and compute risk posture
- Notify security and Ops engineers for immediate action
Integrate with CI/CD pipeline
- Initiate C2VS scans following the deployment of every Dev, QA or Prod environment
- Identify misconfigurations and remediate
Consistency between environments
- Initiate scans concurrently in Active and DR sites
- Identify inconsistent configurations between the two environments
- Remediate before the disaster occurs
Cloud Native App Configuration Overload – The Mis-Configuration Challenge
- Defense-in-depth strategy is leading to new security controls with more configurations
- More environments are created at higher frequencies
- Modern microservice architectures promote more deployable units
- Infrastructure-as-Code and Platform-as-Code creates more configuration properties
- Daily and weekly release candidates are becoming a common practice
- More configuration parameters for performance tuning and efficiency
Do You Treat App Configurations as First Class Citizens?
- Does it take a long time and manual steps to conduct security audits?
- Do you have continuous visibility into your application configurations?
- Do you have the visibility into your database configurations that are specific to your application needs?
- Do you know the gaps in hardening vendor product installations and configurations in your environment?
- Can you assess the risks associated with security misconfigurations at all times?
- Can you compare two application environments?
- Can you track the drift in configurations in your environments?
- Can you understand the context of a misconfiguration and identify the root cause immediately?
If the answer is “NO” to one or more of these questions, C2VS is the answer.
Out-of-the-box Compliance
- Java Stack: Tomcat, Apache web server, Linux OS
- .NET Stack: IIS, .NET Apps, Windows OS
- Databases: Oracle, SQL Server, MySQL, Postgres
- AWS Cloud : EC2, ECS, Lambda, RDS
- AWS Integration: Config, Aurora, Security Hub, Systems Manager
- Red Hat: Ansible Tower and Open Shift
Supported Infrastructue
Environments
- Bare Metal
- Amazon Web Services
Operating Systems
- Red Hat Enterprise Linux
- CentOS
- Amazon Linux
- Ubuntu
Engagement Model
- Capitis professional services team customizes C2VS for your custom applications and CI/CD pipeline
- Configuration compliance coverage increases from a few spot checks to 100% continuous coverage
- Capitis transfers knowledge to your team for on-going operations and maintenance
C2VS is a Highly Customizable Independent Compliance Solution Designed to Identify your Application Specific Misconfigurations and their Root Cause Automatically and Repeatably.
C4S - Analytics & Visualization
- Customizable dashboards
- Filter by scans, environments & compliance categories
- Drill-down capabilities for root cause analysis
- Detailed information for failures
- Summarized errors with risk impact classification
- AWS inventory dashboards linked to C2VS scans
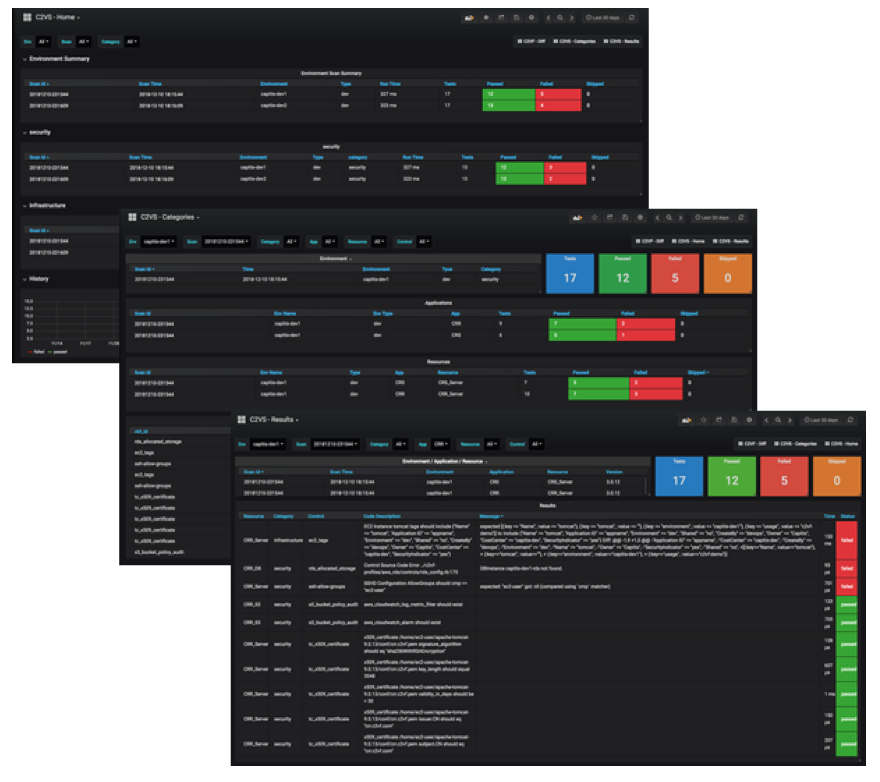
C4S Dashboards
